Wow…It has been a long time since my last post…
I was asked to present a Creating a Windows FE boot disk segment to our local HTCIA chapter. In Part 1, I will go through the steps I used to create a Windows FE bootable CD. With luck, and maybe not so large a gap, Part 2 will go into documenting the use of certain applications within your newly created Windows FE environment.
First some background on Windows FE. An excellent source on the beginnings of Windows FE and build tutorials can be found on Brett Shavers blog:
http://winfe.wordpress.com/2010/05/28/windows-fe/. I also highly recommend downloading (and reading) Brett’s
Users Guide to WinFE. During your read, you will be directed to
http://reboot.pro for current tools to create your Windows FE bootable CD.
For my project/presentation, I downloaded the following items:
1. WinBuilder (version 082)
http://reboot.pro/files/file/4-winbuilder/
2. The WinFE script v2.2 (Public Release) for WinBuilder. I used v2.2 because I am familiar with this script, but as you can see by the link, public release v3.0 is available.
http://reboot.pro/files/file/113-winfe-win7pe-sex64x86-v3-publicreleasescript/
2a. After I completed the training but before I was able to complete this post, and still wanting to make the Ultimate WinFE build, I added an additional script. I have included Colin’s Write Protect Script (wp.script). It can be downloaded here:
https://www.box.com/s/065664cc60bd6bd51464
3. FTK Imager from AccessData
http://accessdata.com/support/adownloads. I actually didn’t download it, I had version FTK Imager 3.0.0.1443 already installed on my machine.
4. VMWare Player, version 4.0.2.
http://www.vmware.com/. Once installed, I launched VMWare Player to get all the fist time pop-up screens out of the way.
5. ProDiscoverBasic edition (U3 install package)
http://www.techpathways.com/DesktopDefault.aspx?tabindex=7&tabid=14
You will also need a Windows7 install DVD. A Win7 Recovery DVD might work, but I wouldn't count on it. Either the x86 bit or x64 bit version will do.
I downloaded WinBuilder.exe, moved it to the root of my c:\ drive, and launched the application. I first had to select a project to download (bottom center pane) before the left pane populated with options. I selected the project: win7pe.winbuilder.net/SE. When the left pane populated, I expanded the Tweaks folder and selected (green check marked) BGInfo.script. I like to know if the computer is connected to a network, and if it is, what is the device’s IP address and other available computer information. I next unchecked Languages, keeping the default English. These are the only changes I made. As you become more experienced with this product, you can design it the way YOU want. When I finished with my ‘fine tuning’, I clicked on the ‘Download’ button.

After about 10 minutes, WinBuilder finished downloading the various scripts and launched. A Window’s pop up informed me WinBuilder was not a trusted application. I chose to run the application and was presented with this screen. What you didn’t see was WinBuilder also created a Projects folder on the root of the C drive.

We next need to do some behind the scenes work and copy an expanded ProdiscoverBasic folder (it was downloaded as a zip file) to our C:\Projects\Win7PE_SE\Apps\Portable\Pstart folder. We will configure the ProDiscover Basic setup later.
Now we need to manually add the WinFE script v2.2 (Public Release) script and the wp.script to WinBuilder. Navigate to your downloaded scripts and copy the scripts to your C:\Projects\Win7PE_SE\Tweaks folder. After the copy process is finished, re-launch WinBuilder.exe. and expand the ‘Tweaks’ folder on the left pane. You should now see, and it should already be green checked, the WinFE (Forensic Environment) and the Write Protect script. As of this writing, it is important the write protect script is listed last (per the scripts installation instructions).
Ok, now that our WinFE script and Write Protect script is seen by WinBuilder, We need to configure the overall environment. The first item is to select the Boot Manager. If you have read my recommended reading, you know we need to change the Boot Manger option in the Main Configuration to ‘Standard’.
The next change is on the Image Configuration tab. Since I am NOT using files from the Windows Automated Installation Kit (AIK), I need to instruct WinBuilder to use the WIMMount driver to extract the files from the Windows 7 installation DVD.
Next, expand the ‘Tweaks’ folder. I checked BGInfo because I want to see various system information displayed on the desktop. If you didn’t check this when downloading your initial project, you will need to be connected to the Internet when you create your WinFE ISO. The BGInfo installation files will need to be downloaded from the Internet at the time of compiling.
Clicking on ‘WinFE (Forensic Environment)’ on the left pane populates the right pane with options. Check ‘Copy Installed FTK Imager from Host Machine’ and navigate to the FTK Imager folder using the ‘Open Folder’ icon. On my 32-bit Windows Operating System, FTK Imager.exe is located at the following location: C:\Program Files\AccessData\FTK Imager\. If you are using a 64-bit OS, FTK Imager.exe is located here: C:\Program Files (x86)\AccessData\FTK Imager\. No other changes are required.

You can click on the ‘WinFE Write Protect Tool’ if you want, but there is nothing to be done here, nor can you make any changes.
Check and Expand ‘Apps’ on the left pane. Expand ‘Portable’, Check and select ‘PStart and Papps’ We are going to add the ProDiscoverBasic tools to our WinFE project. On the right pane:
Add ‘ProDiscoverBasic\Data’ (without the quotes) to the Directory of Apps field.
Add ‘ProDiscoverBasic.exe’ to the Name of exe field.
Check the Start menu box.
Add ‘Forensics’ to the Start menu folder field.
Add ‘ProDiscoverBasic’ to the Name of shortcut field.
Check the ‘Desktop’ box
What you just did was put a ProDiscoverBasic shortcut on the windows desktop in your WinFE environment.
A word of caution. If you are going to be using a Windows 7 x64-bit install DVD, DO NOT add ProDiscoverBasic to this environment, it will not work in x64-bit builds.
The last thing is to check and expand ‘Virtual Test’ and check VMware Emulation. This will boot the newly created WinFE ISO in VMWare Player. This just checks to make sure your build will work.
If you are going to be using a Windows 7 x64-bit install DVD, you will need to make a few more changes to the VMware Emulation configuration settings to make your VMWare session x64 compatible. Click on the VM ‘More Options’ button. Change the ‘Number of processors’ button to ‘automatic, read from system’.

We are FINALLY getting close to create our WinFE ISO image. Now we need to point WinBuilder to our Windows 7 install DVD. Select the ‘Source’ button.

In the Source Directory area, navigate to your Windows 7 install DVD. If you haven’t put the Win7 install DVD in yet, now would be a good time. Once that information has been added, click on ‘Play’

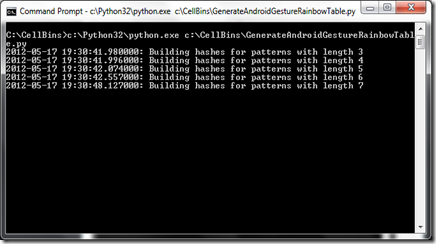
If all goes well with your initial settings, you should get something similar to this display. The process has begun, but this is only half the battle. For now, just sit back and let the script do its work. It will take close to 15 minutes to complete.

This next window will pop up. Don’t let the (Not Responding) fool you. The program has not crashed. Just let it run!

Damn…Got an error message. When I clicked ‘OK’ the process terminated. Now what? You need to fix the cause of the error message. Review the log file to see what caused the error message.

After fixing your error issue, go back to the ‘Main Configuration’ option on the left pane. Click on the ‘Script’ button, right pane in upper left. Now we need to clear the temporary files. Click the ‘Clear Temporary Files’ to perform this task.

Now you’re ready to try it again. Click the ‘Play’ button once again and cross your fingers. If you are presented with a VMWare Player window like this….

CONGRADULATIONS!!! It works. You see before you the Write Protect script telling you the 2GB VMWare created hard drive is read only. If you were using this on a regular computer, all storage media should be listed as read-only. If the drive is not listed, there might be a driver issue or hardware problem. When you click ‘Close’, the FE environment will continue to boot up. Windows drivers will continue to load. If you get an error at this point, it will be a driver issue. Its not uncommon on newer machines to get a network device error. This just means the default drivers within Windows do not support this device. No problem, unless you need network connectivity. If you need a working network device are need to add a specific driver for a piece of hardware you will be using, read the documentation, it discusses how to add additional drivers to the WinBuilder WinFE creation process. When the system has finished booting, you will be presented with your normal Windows GUI desktop.
Ok, now I want to burn my WinFE ISO image to a CD/DVD. Your newly created ISO image is located in your C:\ISO folder. Depending on the OS version, you will either have a Win7PE_x86.ISO or Win7PE_x64.ISO or both image files in this folder. Using your favorite ISO burning software, these are the ISO images files you need to create your Win7 bootable CD\DVD.
I recommend you immediately rename the ISO to Win7
FE_x86.ISO (or x64) and move it to a different directory. If you were to create an additional WinFE ISO images using the same Windows7 install DVD, the newly created ISO file overwrites the old ISO file(without asking permission).
That’s it for now….Enjoy you new WinFE boot disk.
Don’t forget to do some experimentation and add additional portable apps to your WinFE environment.